Overview
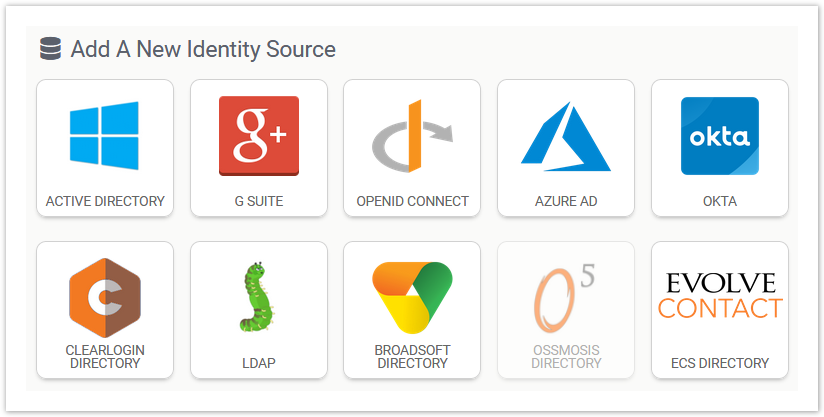
An Identity Source is a structured directory of objects (users, groups, computers, etc.) that Clearlogin uses to look up and verify the validity of an authentication attempt. Clearlogin has its own internal directory that can be used as an identity source, or Clearlogin can be configured to use one or more of the following identity sources:
Identity Source Priority
Identity Source Priority determines the order in which a user's authentication attempt will hit each Identity Source. Clearlogin will go through each identity source until the user's credentials are matched with the credentials in an identity source. If no matching credentials are found in any of the identity sources, then the authentication attempt will fail.
There are 10 priority slots for your identity sources with a priority of 1 being the highest priority and 10 being the lowest priority. If you set two or more identity sources to the same priority, the identity sources will be queried from the oldest creation date (first) to the newest creation date (last).
Best practice is to set a priority order with the largest identity source with the highest priority and the smallest identity source with the lowest priority.
Identity Source Access Tags are used to scope Access Rules and Applications to the user accounts in the identity source. Under normal conditions you would use the name of an Identity Source as the name of the Access Tag. However, this can be overridden with a custom name for the access tag.
For example, if the identity sources have long descriptive names, you can abbreviate them with a custom name for the access tags.